Nowadays, you find smart technologies all around us: in vehicle control systems, smart homes, smart cities, but also in household appliances, car keys, payment cards, or even public transport passes. These devices belong to the category of Internet of Things (IoT) and embedded systems, which are highly vulnerable to hacker attacks.
“Our students learn how to carry out these attacks and how to defend against them. The practical knowledge of these attacks is crucial for students to effectively protect devices against these types of relatively common attacks in practice. They then become experts in the security and protection of embedded systems,” says Dr.-Ing. Martin Novotný, head of the lab.
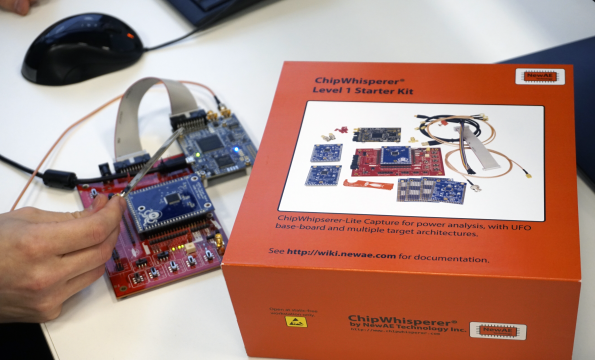
An example of such security threats is side-channel attacks, through which the attacker tries to obtain information for subsequent possible misuse. The attacker’s goal is usually to take control of the device or obtain the user data (for example, to find out the encryption key used or reveal the PIN code). The behaviour of the compromised device often remains intact, and such attack can thus take place completely unnoticed. To counter these attacks and defend against them effectively, students must first try them out in practice. In the lab, students learn to implement side-channel attacks, prepare the device and measure its power consumption, analyze the data, and lastly break the cryptosystem. They thus learn to identify specific threats and ways to prevent such attacks and protect the system. In the coming year, the lab plans to expand the training to include attacks exploiting electromagnetic radiation as well as active attacks consisting of fault injections.
The teaching equipment is financed from faculty resources and the teaching is co-financed by the project of the Ministry of Education, Youth and Sports from the Operational Programme Research, Development and Education, ESF Call for Universities II, named CTU ESF II Project - Introduction of practical teaching of selected types of cryptanalytic attacks.